Here's everything to know about 'WannaCry' ransomware; measures & more
The 'WannaCry' ransomware has attacked about 150 countries across the world but little is being talked about what is this cyber attack about,which countries are affected and how to prevent it. Here's everything to know about 'WannaCry' ransomware.

Highlights:1. The 'WannaCry' ransomware attacked the computers around the world on May 12
2. The virus locks access to user files and demands money -- in the form of the virtual currency Bitcoin -- in order to decrypt them
3. Victims include hospitals in Britain, the Spanish telecoms giant Telefonica, French carmaker Renault, US package delivery company FedEx, among others
Since the news of a cyber-attack 'WannaCrypt' or 'WannaCry' ransomware broke last Friday, the governments and companies across the world have been asking people to update Microsoft's Window XP software to prevent their machines from getting infected with the virus.
According to AFP report dated May 14, computers around the globe were hacked beginning last Friday using a security flaw in Microsoft`s Windows XP operating system, an older version that was no longer given mainstream tech support by the US giant.
The so-called 'WannaCry' ransomware locks access to user files and demands money -- in the form of the virtual currency Bitcoin -- in order to decrypt them, it said.
ALSO READ: Cyber attack hits 200,000 in at least 150 countries: Europol
It is the largest ransomware attack observed in history.
High-profile victims include hospitals in Britain, the Spanish telecoms giant Telefonica, French carmaker Renault, US package delivery company FedEx, Russia`s interior ministry and the German rail operator Deutsche Bahn, the AFP report said.
Experts said the ransomware programme appears to support dozens of languages, showing that the hackers wanted to corrupt networks worldwide.
According to European Union's police agency Europol the latest cyber-attack is set to have impacted 200,000 victims in at least 150 countries and the number would increase when people return to work on Monday, Reuters reported.
Europol Director Rob Wainwright told ITV`s Peston on Sunday programme that what was unique about the attack was that the ransomware was used in combination with "a worm functionality" so the infection spread automatically.
"The global reach is unprecedented. The latest count is over 200,000 victims in at least 150 countries, and those victims, many of those will be businesses, including large corporations," Reuters said quoting Rob, as saying.
"At the moment, we are in the face of an escalating threat.The numbers are going up, I am worried about how the numbers will continue to grow when people go to work and turn (on) their machines on Monday morning," he added.
ALSO READ: Renault stops production at some sites after cyber attack
Due to ransomware cyber attack, France's auto company Renault had stopped production at several sites on Saturday in order to prevent the spread of a global cyber attack that hit its computer systems on Friday, Reuters reported citing the company's spokesman, as stating.
The French carmaker said on Sunday that it expected to resume normal production in factories on Monday that were hit by cyber attack.
Similarly, Japan's automaker Nissan too reported on Saturday that its manufacturing plant in the UK was affected by the cyber attack.
“Like many organisations, our UK plant was subject to a ransomware attack affecting some of our systems on Friday evening. Our teams are working to resolve the issue," Reuters reported quoting the company's spokesman, as saying.
Even as companies around the globe are preparing for an imminent cyber attack, the computers of two village panchayats in Kerala were hit with messages demanding $300 in virtual currency to unlock the files, cited IANS report.
Officials who on Monday opened the office computer at the Thariyode panchayat office in the hilly district of Wayanad found that four of their computers have been hacked.
"The four computers were switched on as usual and they were unable to open the any document files as the virus displayed messages demanding a payment of $300 in virtual currency Bitcoin to unlock files and return them to the user. We have informed the district authorities about this," IANS reported quoting Santhosh, a panchayat official, as saying.
ALSO READ: IT Ministry reaches out to RBI, others against Wanna Cry ransomware
The Indian government's Ministry of IT and Electronics has reached out to key stakeholders like RBI, National Payments Corporation of India (NPCI), NIC and UIDAI (Aadhaar) to advise them to protect their systems against 'Wanna Cry' ransomware to ensure that the digital payments ecosystem in the country is protected, according to PTI report.
Automated teller machines (ATMs) of some banks may have been affected by the recent ransomware attack globally, Bloomberg reported citing government official as saying.
Advisable to avoid using ATMs for couple of days, the official said,asking not to be identified citing rules on speaking to the media people should not reply to suspicious emails from banks, the report said.
Experts fear the situation could further aggravate as a number of computers in India run on the older operating systems and have not been updated yet.
"This attack is perhaps the largest, most widespread and contiguous malware attack in history as the attackers have used a flaw in Microsoft software to infiltrate unguarded systems. It is important that users keep their systems updated and take a proactive approach to security rather than a reactive one," PTI said quoting Pradipto Chakrabarty, Regional Director at CompTIA India, as saying.
Replying to cyber attack, Microsoft in its blog said," Today, many of our customers around the world and the critical systems they depend on were victims of malicious “WannaCrypt” software. Seeing businesses and individuals affected by cyberattacks, such as the ones reported today, was painful."
"Microsoft worked throughout the day to ensure we understood the attack and were taking all possible actions to protect our customers," it added.
Microsoft in a blog further said,"We are taking the highly unusual step of providing a security update for all customers to protect Windows platforms that are in custom support only, including Windows XP, Windows 8, and Windows Server 2003. Customers running Windows 10 were not targeted by the attack today."
ALSO READ: Carmaker Nissan says UK plant hit by cyber attack
What is Ransomware?
According to Microsoft website, ransomware are of different types and they can target any PC users, whether it’s a home computer, endpoints in an enterprise network, or servers used by a government agency or healthcare provider.
Ransomware can:
1.Prevent you from accessing Windows.
2.Encrypt files so you can't use them.
3.Stop certain apps from running (like your web browser)
Ransomware will demand that you pay money (a “ransom”) to get access to your PC or files, cited the company's website.
There is no guarantee that paying the fine or doing what the ransomware tells you will give access to your PC or files again.
ALSO READ: Cyber attack techniques used by US-led coalition to be imitated by other countries
What is 'WannaCry' Ransomware?
The ransomware called 'WannaCrypt' or 'WannaCry' encrypts the computer's hard disk drive and then spreads laterally between computers on the same LAN. The ransomware also spreads through malicious attachments to emails, according to India's Cyber Swachhta Kendra website.
In order to prevent infection, users and organisations are advised to apply patches to Windows systems as mentioned in Microsoft Security Bulletin MS17-010, it said.
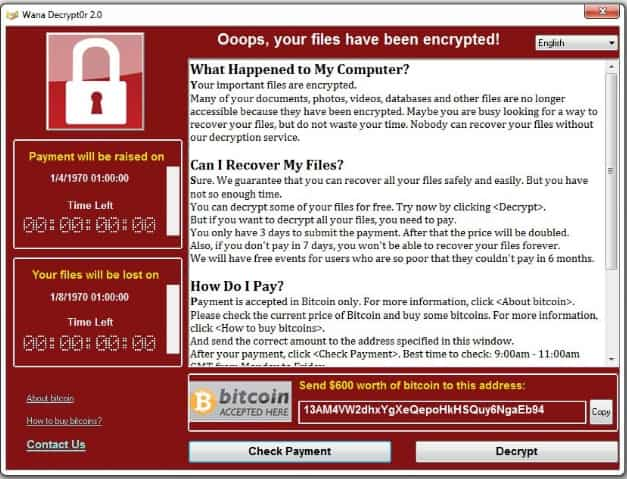
After infecting, this Wannacry ransomware displays following screen on infected system:
WannaCry encrypts files with the following extensions, appending.WCRY to the end of the file name: .lay6,.sqlite3, .sqlitedb, .accdb, .java, .docx, .doc, etc.,
The file extensions the malware is targeting contains certain clusters of formats including commonly used office file extensions .ppt, .docx, .doc, .xlsx, etc.,
Measures To Prevent 'Wanna Cry' Ransomware
The Indian government's Ministry of IT and Electronics has issued some measures to protect computer networks from ransomware infection or attacks:
1. In order to prevent infection users and organisations are advised to apply patches to Windows systems as mentioned in Microsoft Security Bulletin MS17-010
2. Microsoft Patch for Unsupported Versions such as Windows XP,Vista,Server 2003, Server 2008 etc. http://www.catalog.update.microsoft.com/Search.aspx?q=KB4012598
3.To prevent data loss Users & Organisations are advised to take backup of Critical Data
4.Block SMB ports on Enterprise Edge/perimeter network devices [UDP 137, 138 and TCP 139, 445] or Disable SMBv1. https://support.microsoft.com/en-us/help/2696547
09:53 AM IST





 Renault expects return to normal production on Monday after cyber attack
Renault expects return to normal production on Monday after cyber attack Cyber attack hits 200,000 in at least 150 countries: Europol
Cyber attack hits 200,000 in at least 150 countries: Europol Carmaker Nissan says UK plant hit by cyber attack
Carmaker Nissan says UK plant hit by cyber attack IT Ministry reaches out to RBI, others against Wanna Cry ransomware
IT Ministry reaches out to RBI, others against Wanna Cry ransomware Cyber attack techniques used by US-led coalition to be imitated by other countries
Cyber attack techniques used by US-led coalition to be imitated by other countries